Thought leadership content published as local static pages.
Blog content is synced from Wix Blog, normalized, and rendered into additive routes only.

IAM for AI: 4 Steps to Secure and Futureproof Agentic Systems
As AI evolves from reactive chatbots into autonomous agents that take real-world actions, Identity and Access Management must evolve with it. Four foundational steps—machine identity, least privilege, real-time monitoring, and a governance maturity model—form the security backbone every enterprise needs before deploying agentic AI at scale.
Open page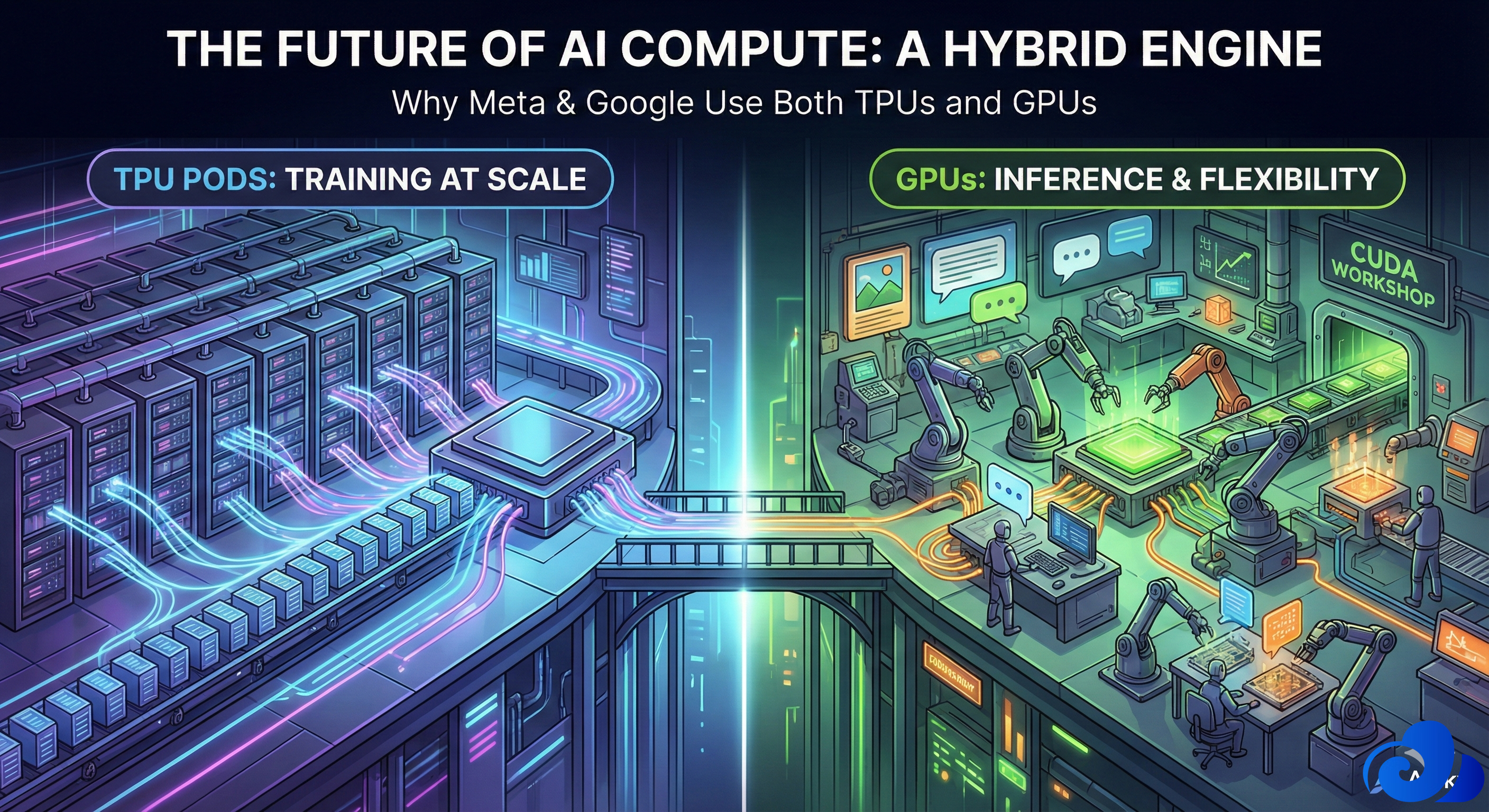
Why Meta Is Turning to Google TPUs And Why NVIDIA Is Still Market Leader
A story about two very different machines shaping the future of AI. In late 2024, the AI hardware world witnessed a quiet but significant shift: Meta began training large portions of its Llama 3 and 4 models using Google’s TPU (Tensor Processing Unit) pods. For a company that famously buys hundreds of thousands of NVIDIA GPUs, this move was surprising. Why would Meta—an empire built on GPUs—suddenly embrace Google’s custom silicon? To understand this, you have to look at the fundamental...
Open page
Understanding Cache-Augmented Generation (CAG)
CAG shifts the focus from dynamic retrieval to offline precomputation. It exploits the KV caching mechanism of transformer-based LLMs. Here, intermediate activations (keys and values) from the attention layers are stored for reuse, speeding up inference. Key Components and Flow Preprocessing Phase : The knowledge base, which may include documents, knowledge bases, or database extracts, is fed into the LLM. This allows the model to compute and store KV caches. The result is a "preloaded...
Open page
Techniques for enhancing LLM’s
Techniques for enhancing LLM’s The provided diagram compares two primary techniques for enhancing Large Language Models (LLMs) with external or domain-specific knowledge: Retrieval-Augmented Generation (RAG) in the top section and Fine-Tuning in the bottom section. It uses icons and flow arrows to illustrate the processes, with labels like "Gemini" (likely referring to Google's LLM) and various data sources. This setup is common in AI systems to improve response accuracy, relevance, and...
Open page
The Evolution of Artificial Intelligence: Understanding Agentic AI
The Transformative Power of AI Artificial intelligence is evolving rapidly. Three main concepts—Large Language Models (LLMs), Generative AI, and Agentic AI—are changing how businesses, developers, and users interact with intelligent systems. At the center of this AI landscape are LLMs like GPT-4. These models are trained on large datasets to recognize patterns, solve complex problems, and communicate in ways that resemble human speech. They serve as the cognitive foundation, helping systems...
Open page
Industry Insight: Cloud Security Is Shifting Left; Here’s What That Means for Enterprise
n a shift left model, security is no longer the sole domain of a separate security team. Instead, developers are empowered and expected to take ownership of security. This involves using automated tools to scan code for vulnerabilities as it's written and implementing security best practices throughout the development process. By doing so, security keeps pace with development, allowing teams to build and deploy software that is both innovative and secure, without sacrificing speed.
Open page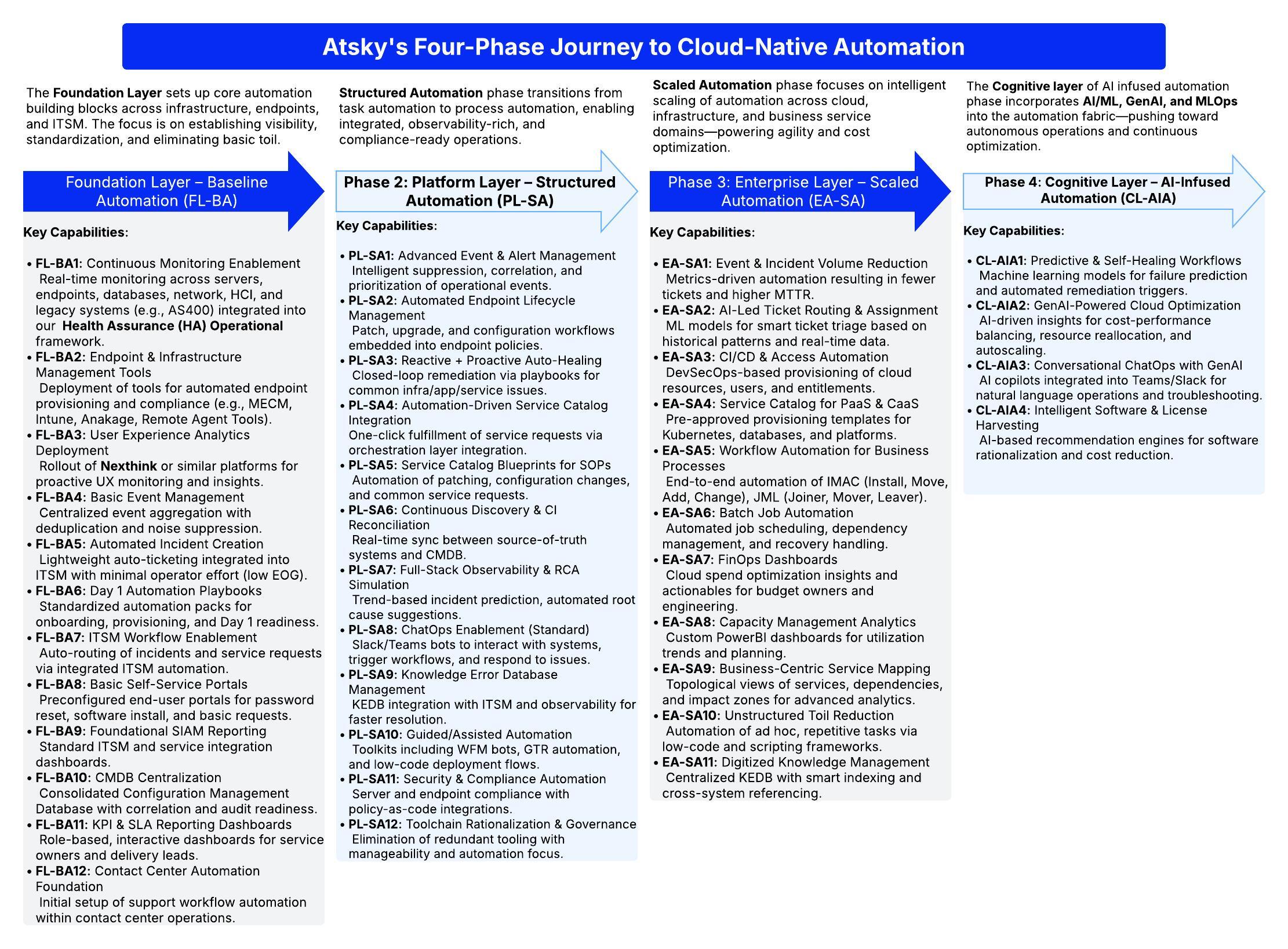
Modern DevOps in the Era of Cloud 2.0: The Power of Automation in Driving Transformation
As businesses face the pressures of quick innovation, strong infrastructure, and secure growth, traditional DevOps alone is not enough....
Open page
Atsky’s Take on Cloud-Native Transformations: What Works, What Doesn’t, and How We Get It Right
Let’s be honest. "Going cloud-native" sounds impressive, but it's actually a complex and high-stakes process. We’ve seen this firsthand....
Open page
Webhooks
Architectural Style & Patterns: Webhooks are a pattern for server-to-server callbacks over HTTP. In essence, a webhook occurs when...
Open page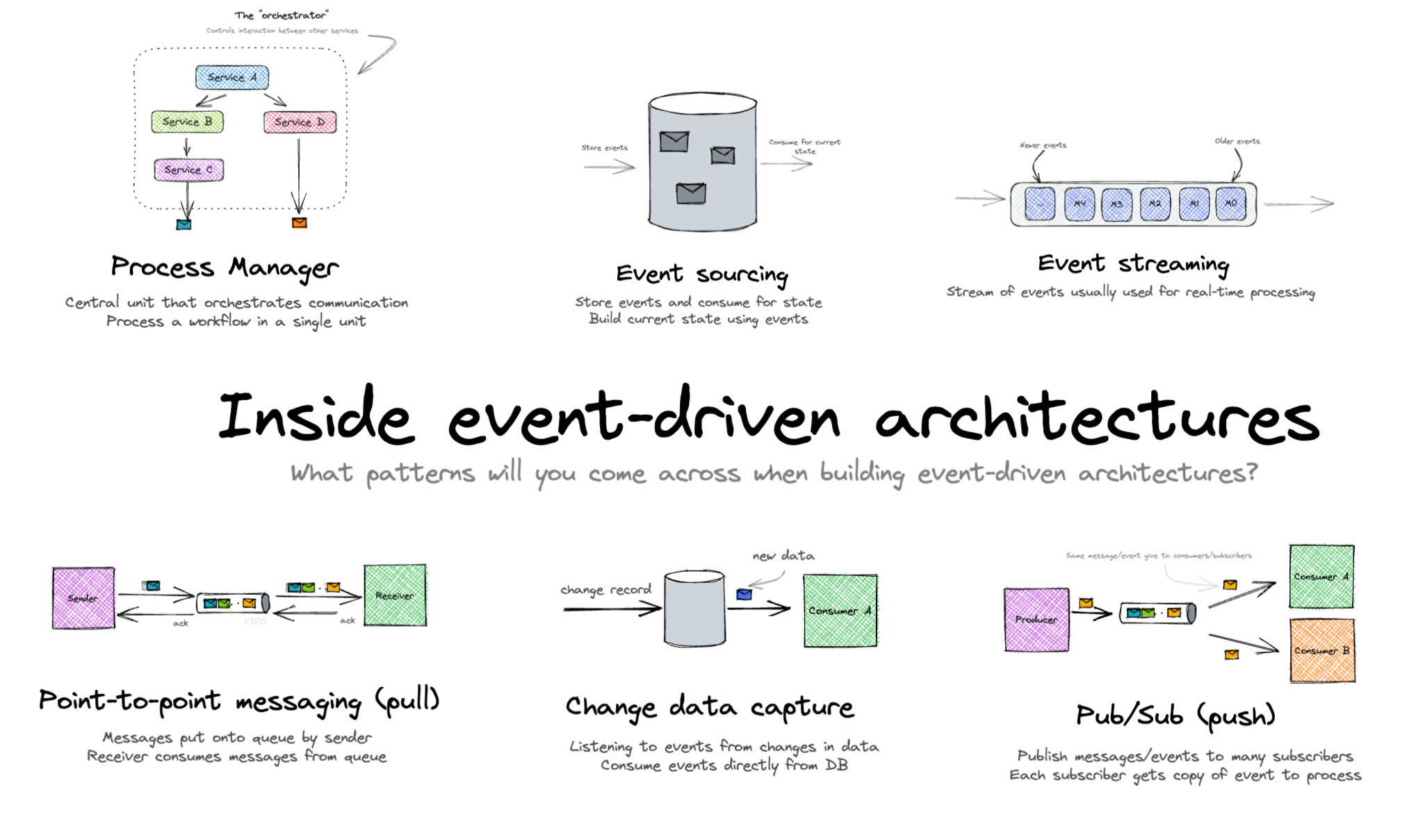
EDA (Event-Driven Architecture)
Architectural Style & Patterns: Event-Driven Architecture (EDA) is a design paradigm rather than a specific protocol. It involves...
Open page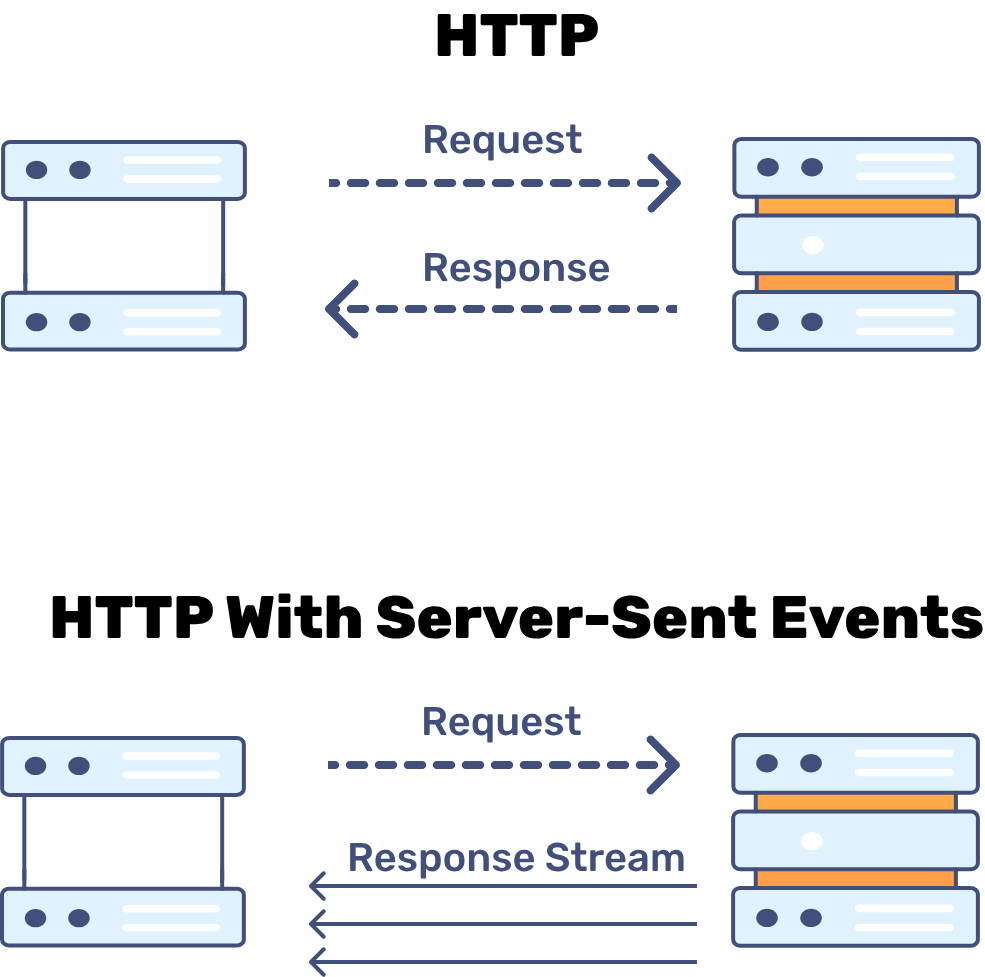
SSE (Server-Sent Events)
Architectural Style & Patterns: Server-Sent Events (SSE) , sometimes known by its API name EventSource, is an HTTP-based protocol that...
Open page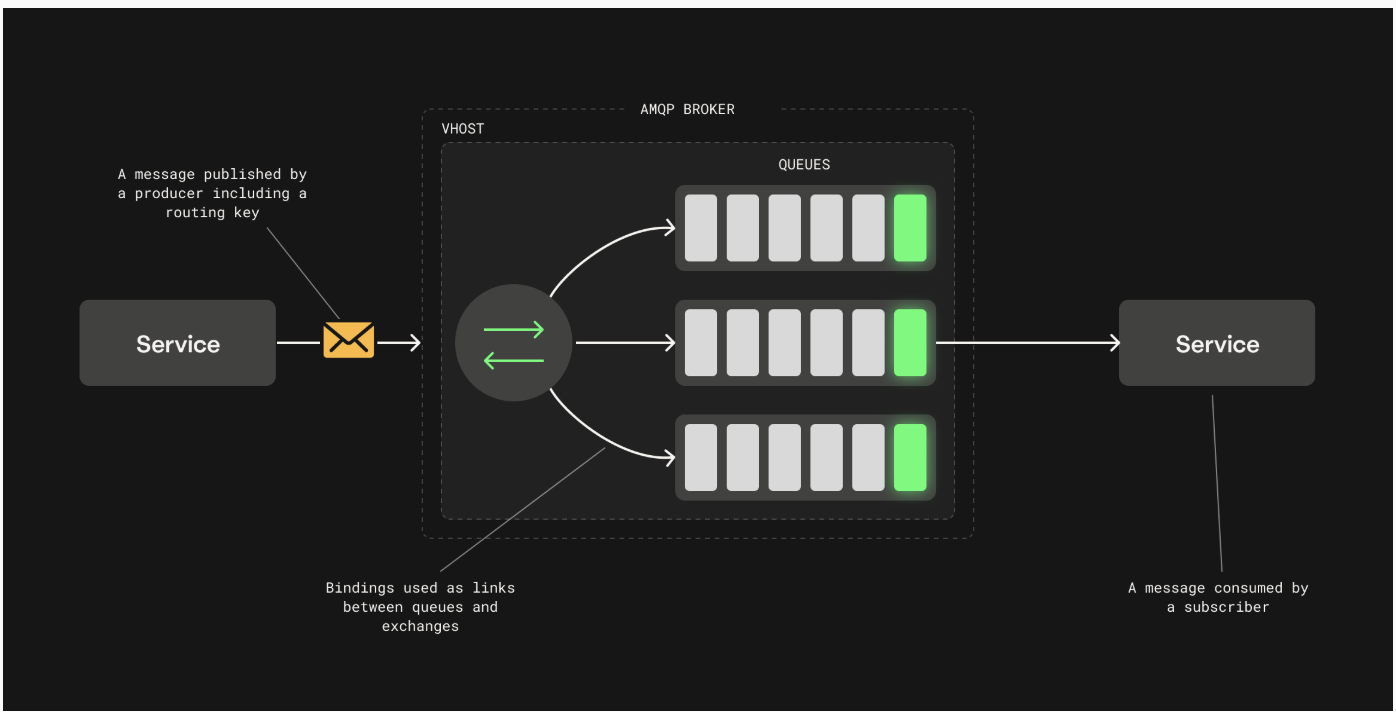
AMQP
Architectural Style & Patterns: AMQP (Advanced Message Queuing Protocol) is an open standard for enterprise messaging, designed to...
Open page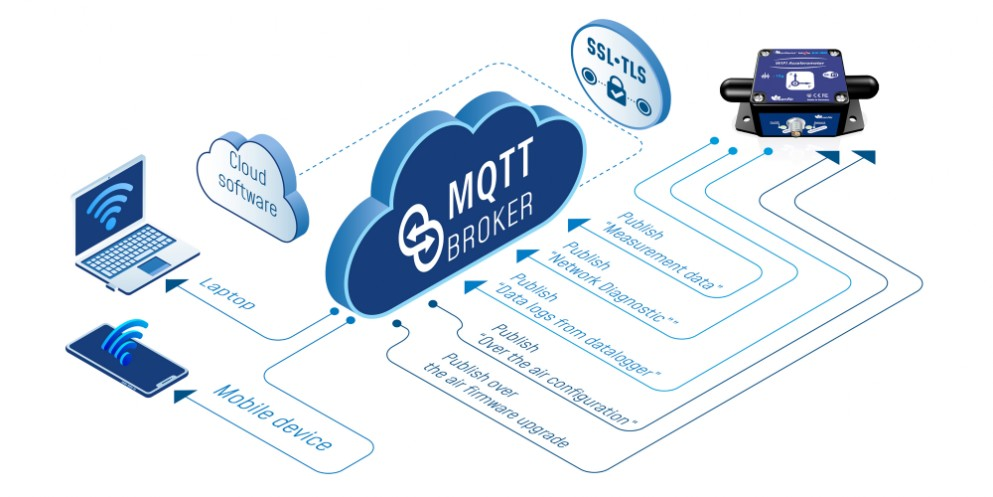
MQTT
Architectural Style & Patterns: MQTT (Message Queuing Telemetry Transport) is a lightweight publish-subscribe messaging protocol,...
Open page
gRPC
Architectural Style & Patterns: gRPC is a modern, high-performance RPC (Remote Procedure Call) framework open-sourced by Google. It...
Open page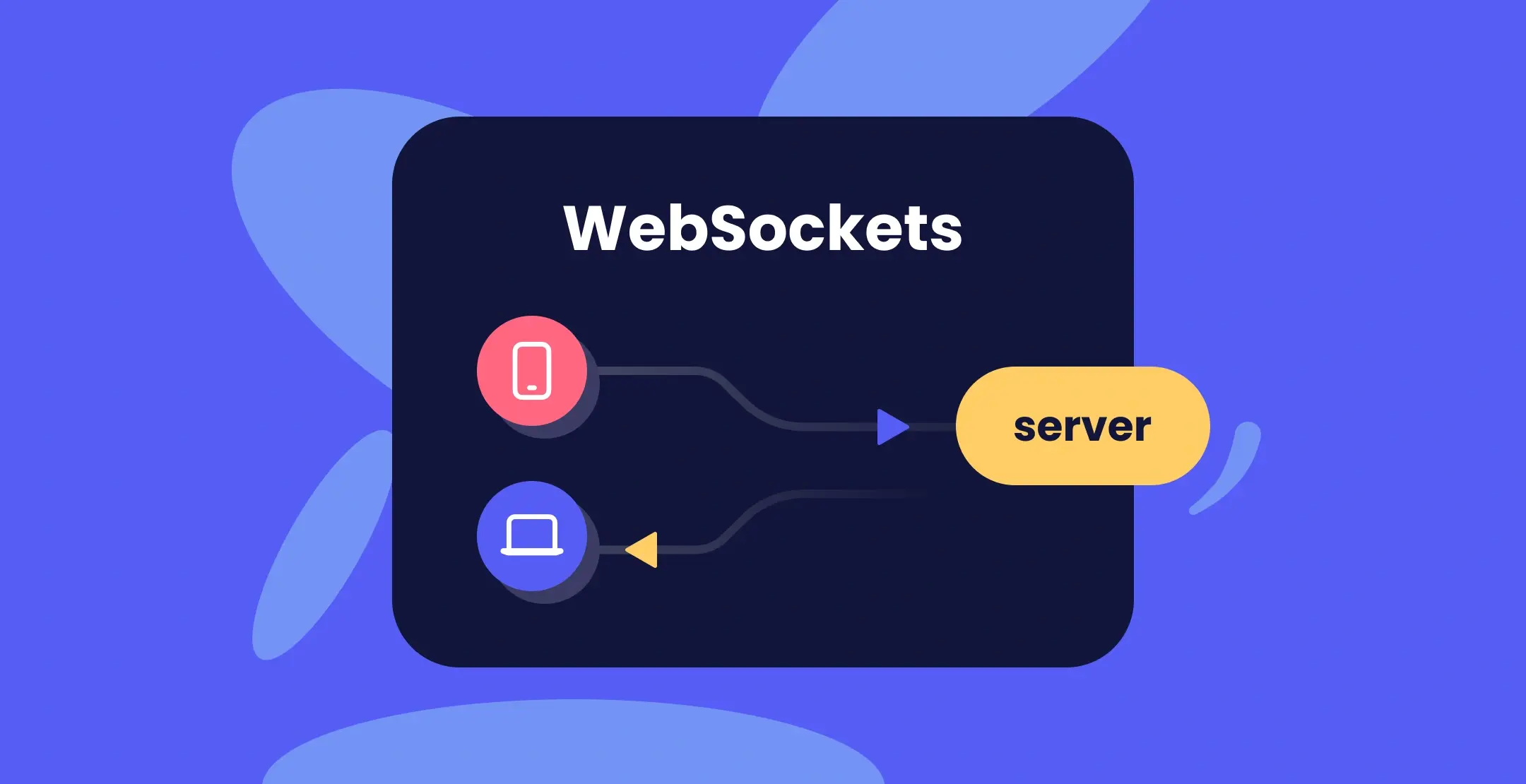
WebSockets
Architectural Style & Patterns: WebSockets enable a persistent, full-duplex communication channel over a single TCP connection....
Open page
SOAP (Simple Object Access Protocol)
Architectural Style & Patterns: SOAP is a protocol that predates modern REST/GraphQL and follows a RPC-style or document-style...
Open page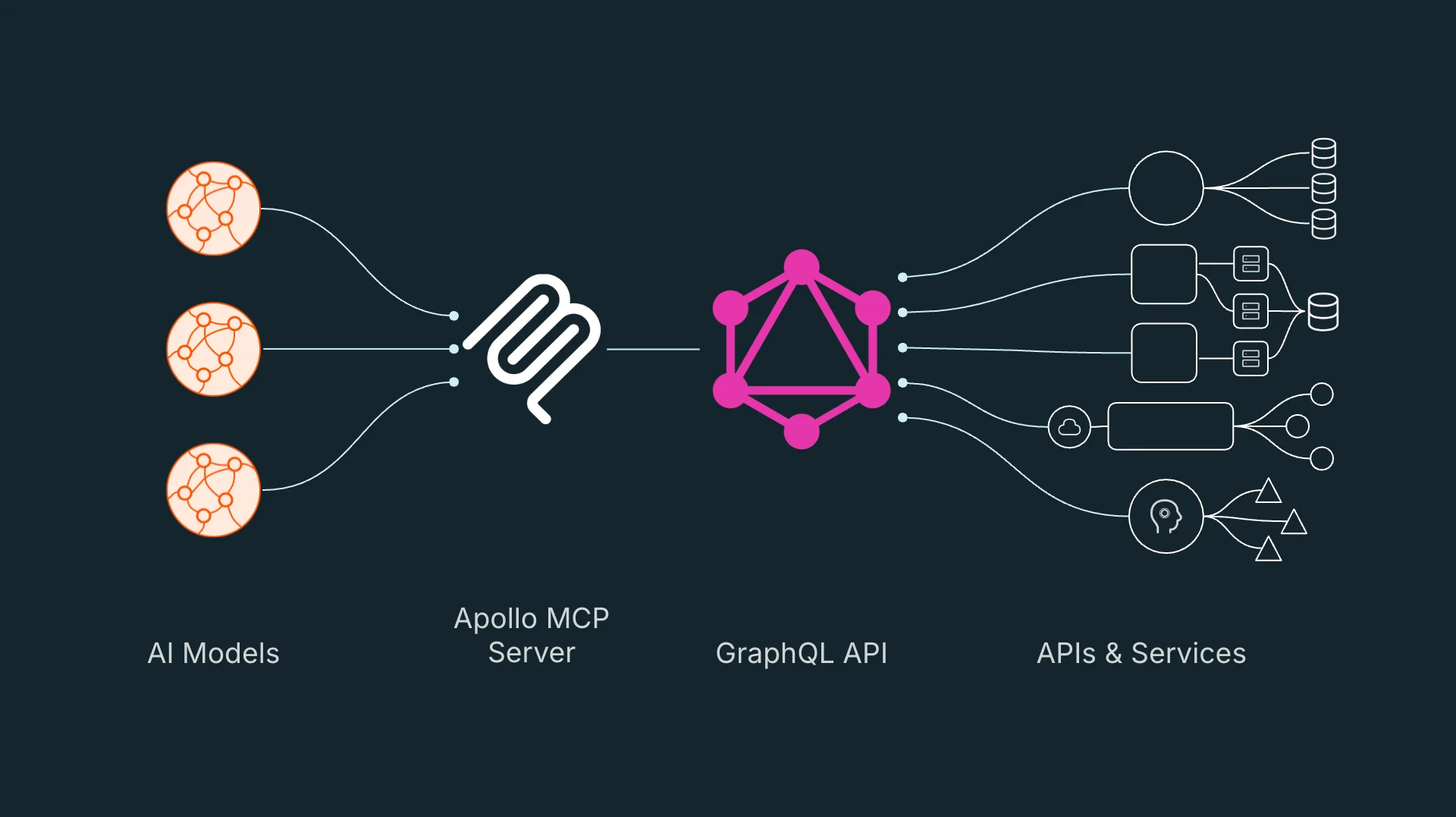
GraphQL
Architectural Style & Patterns: GraphQL is a query language and runtime for APIs that departs from fixed endpoints. It still follows a...
Open page
REST (Representational State Transfer)
Architectural Style & Patterns: REST is an architectural style that operates over HTTP with a stateless, client-server model. It...
Open page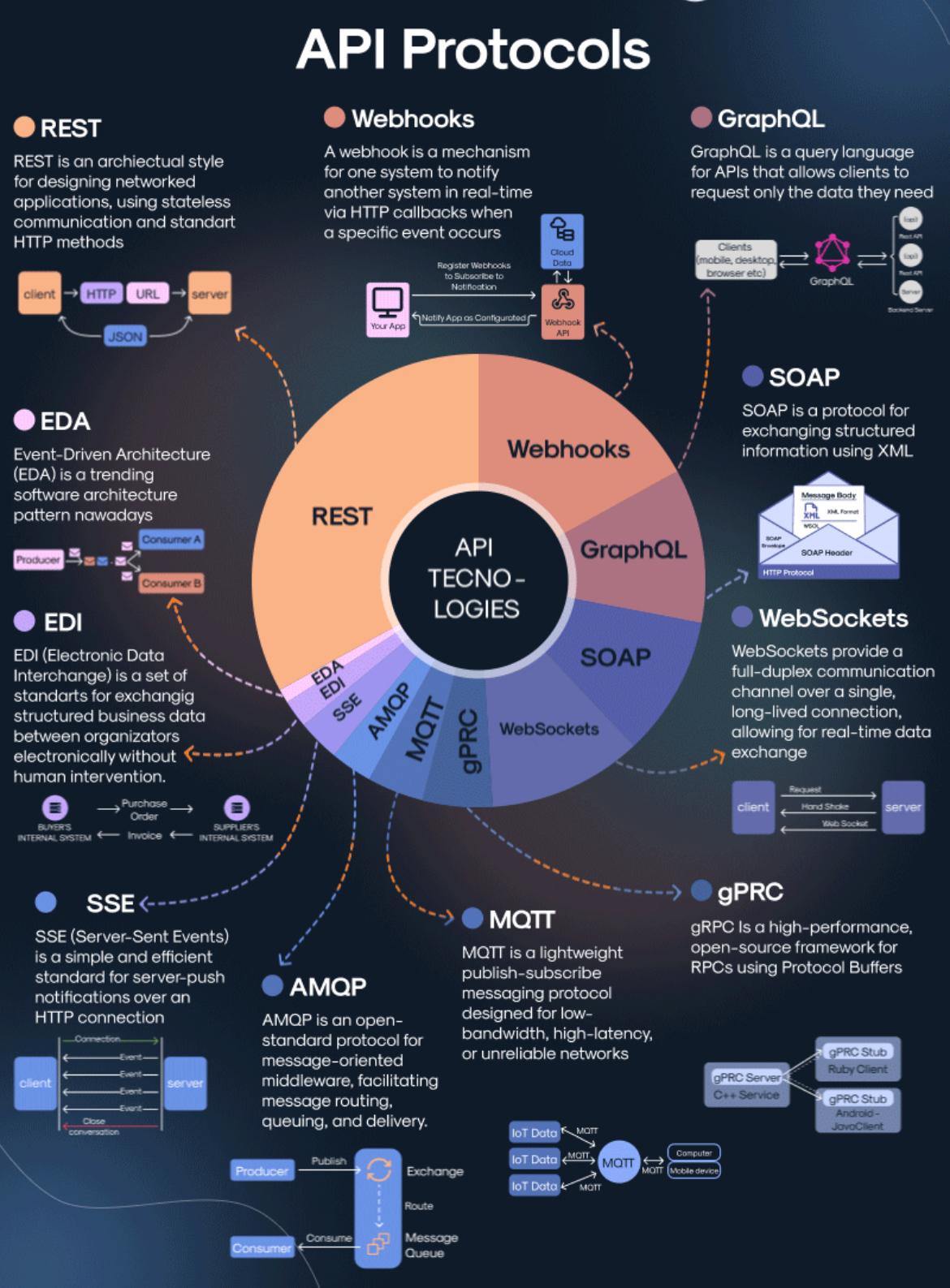
Comparison of API Protocols for Modern Architecture Styles
Application Programming Interface (API) communication is the backbone of modern software integration. From web and mobile apps to...
Open page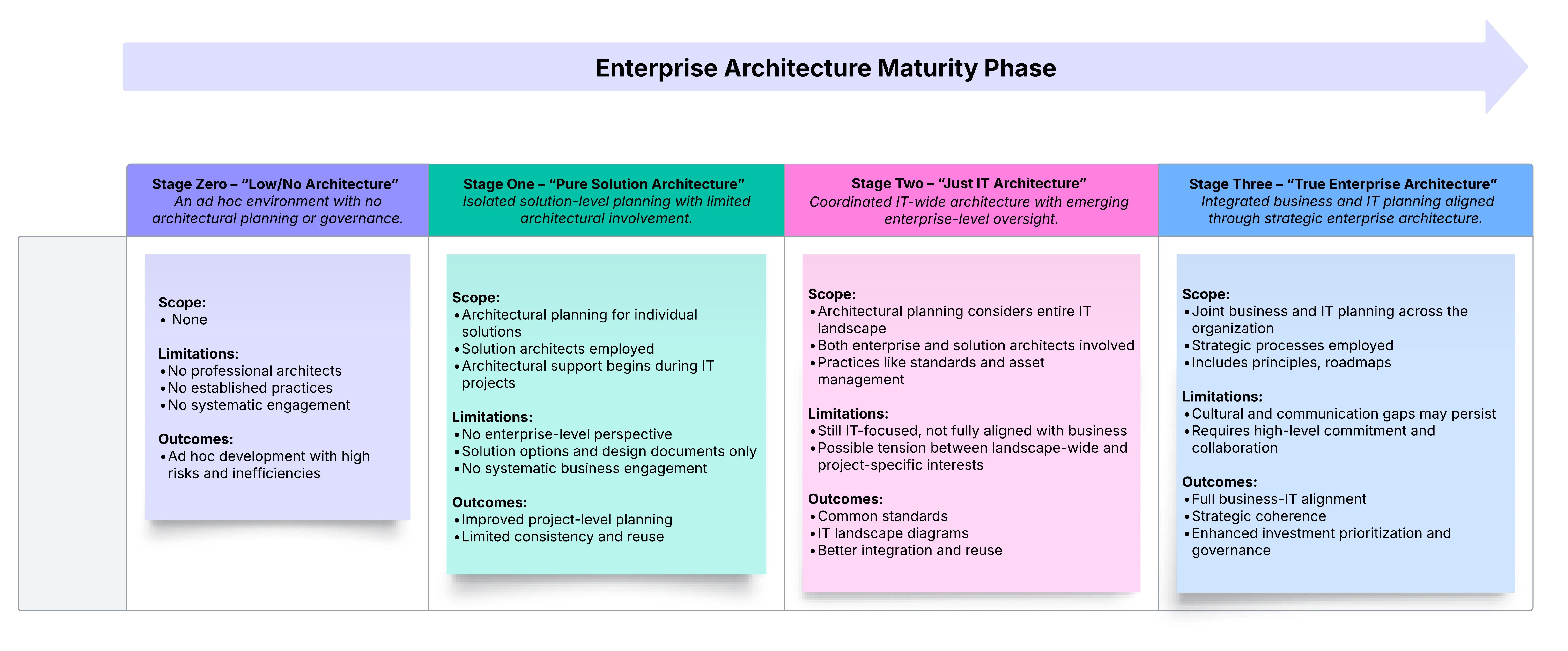
Navigating Enterprise Architecture (EA) Maturity: From Fragmented to Strategic Clarity
Introduction Enterprise Architecture (EA) has evolved from a niche IT discipline into a strategic function that directly influences...
Open page
Guide to API Protocols
Understanding the Key Technologies, Usage & Market share APIs (Application Programming Interfaces) play a crucial role in the digital...
Open page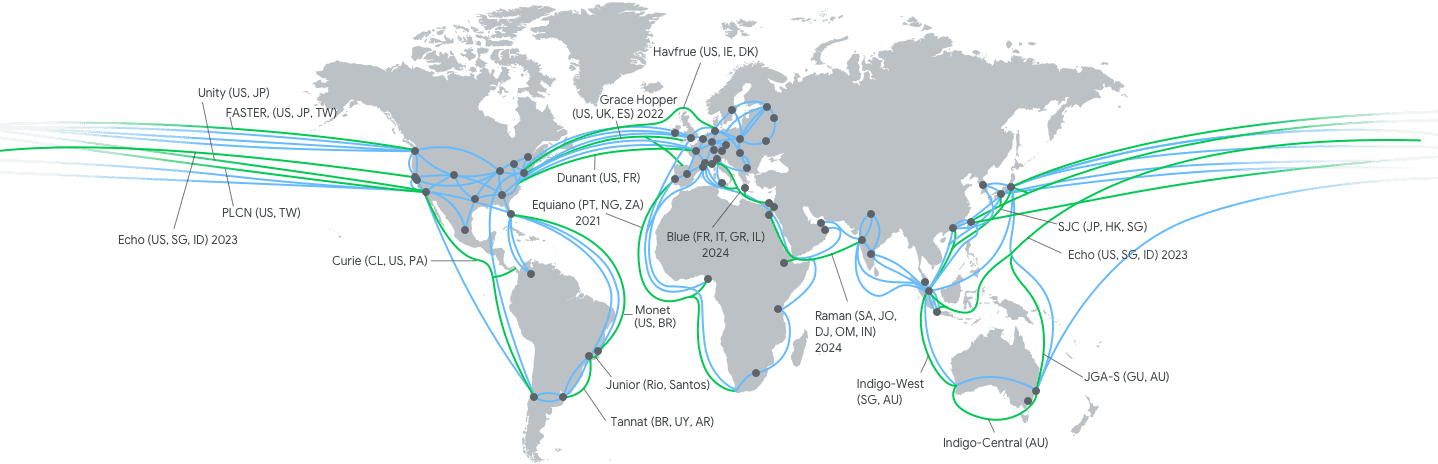
Building an Active-Active Latency-Based Application Across Multiple Regions
In the hyper-connected world we live in, economies of scale for businesses rely on web applications to serve users around the world. The...
Open page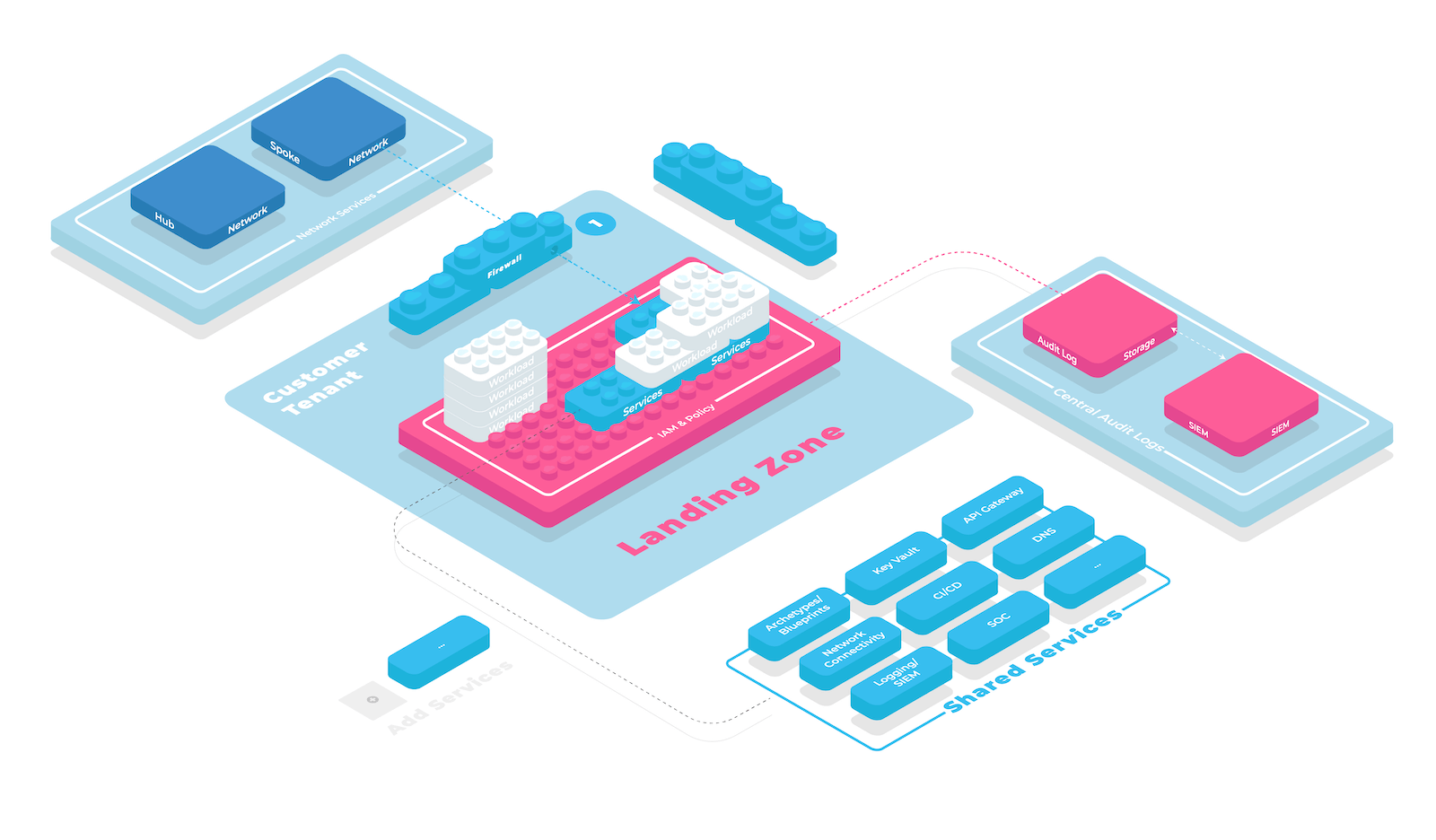
Know why Secure Landing Zones are Non-Negotiable in Cloud Adoption
Increasing cloud footprint and adoption of cloud services becoming a strategic imperative for businesses looking to stay competitive and...
Open page
Scaling AI - The Big Bet on Computing Power and the Future of Cloud Services
The recent valuation of Safe SuperIntelligence at $5 billion, under the leadership of Ilya Sutskever, highlights the race towards AI, and...
Open page
Pioneering GitOps in Complex Cloud Environments
Nowadays, there is a growing need for efficient, scalable, and reliable software deployment processes. As businesses move to the cloud,...
Open page
Transforming Enterprises with Secured Cloud Automation: Atsky’s Success Stories
As enterprises increasingly shift to the cloud, the need for secure, automated, and scalable solutions has never been more critical. At...
Open page
The Birth of Atsky: From Traditional IT to Cloud InnovatorIntroduction
Atsky started with a simple but powerful idea: to help businesses easily embrace the future with cloud technologies. Founded by a team of...
Open page
Navigating the NIS2 Directive: A Guide
The digital landscape is evolving rapidly, and with it, the threats that organisations face in terms of cybersecurity are becoming more...
Open page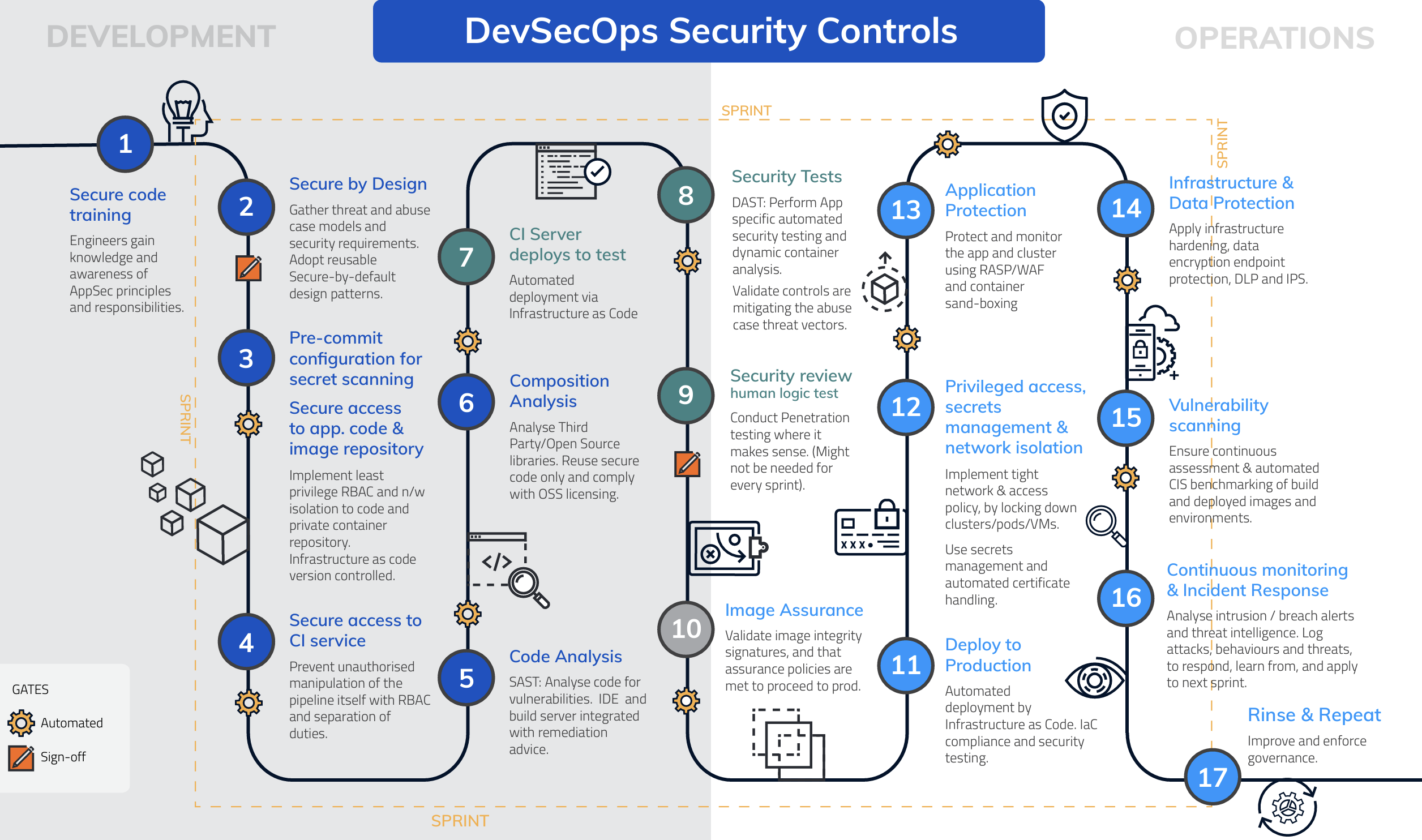
Atsky Initiative: Navigating the Complexities of Modern Architectures
Modern technological frameworks like containers and Kubernetes bring forth immense advantages but also pose distinctive challenges. In...
Open page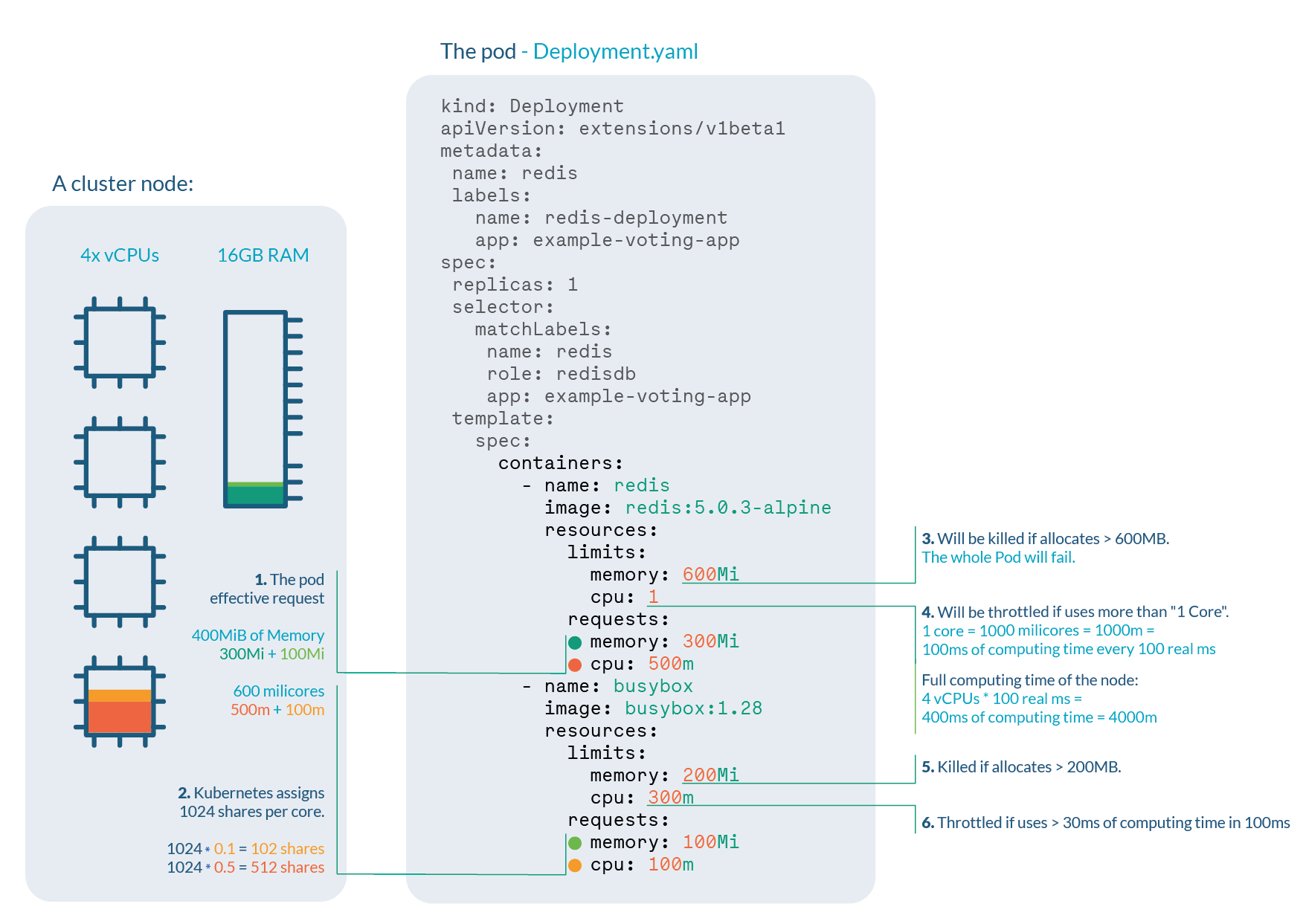
In Kubernetes, What Should I Use as CPU Requests and Limits?
If you're working with Kubernetes, you're probably already aware of the importance of properly managing your cluster's resources. When it...
Open page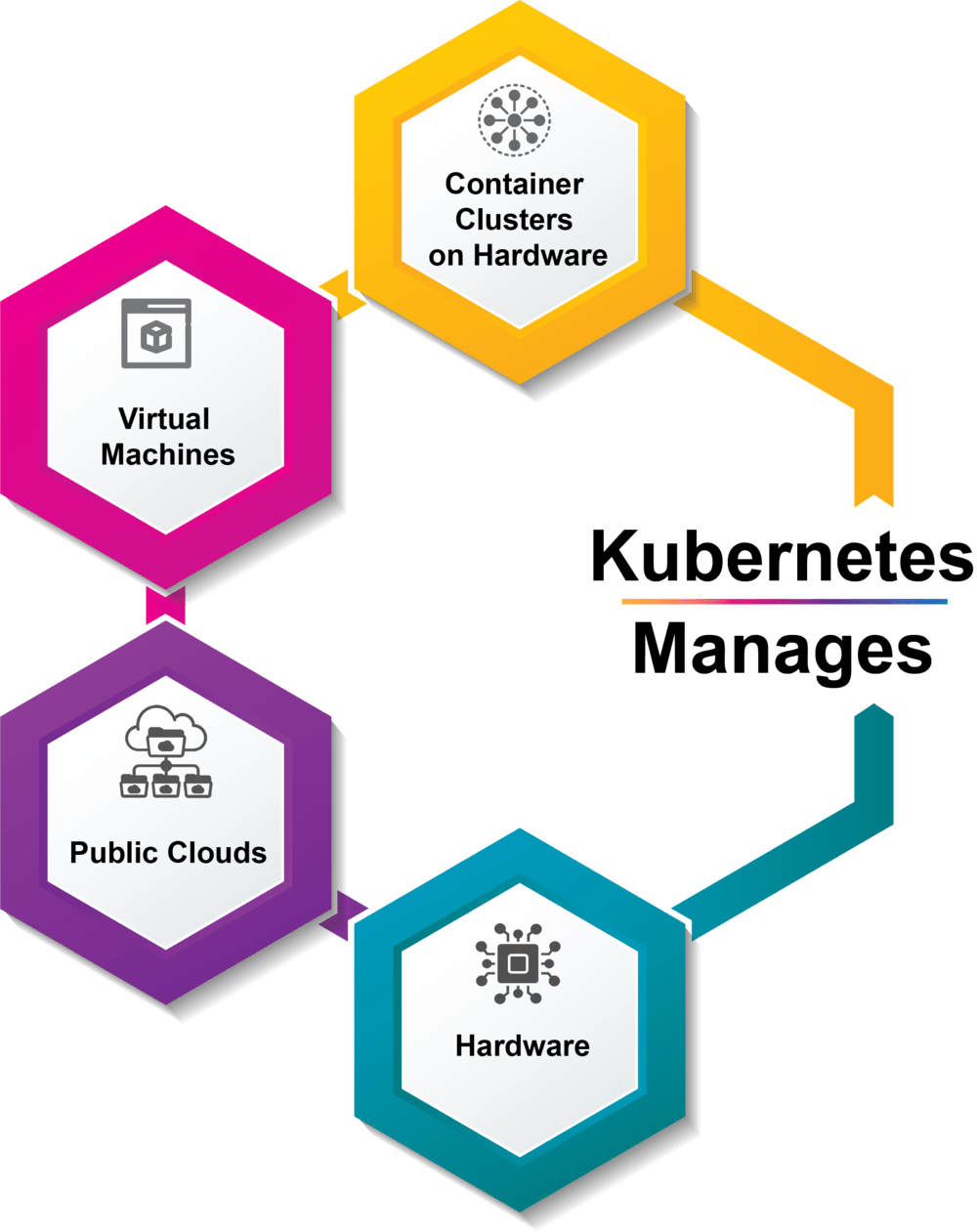
A Simplified Guide to Kubernetes Management and Tools
Overview of Kubernetes Management Managing a Kubernetes cluster isn't a walk in the park—it requires specialized tools that help you get...
Open page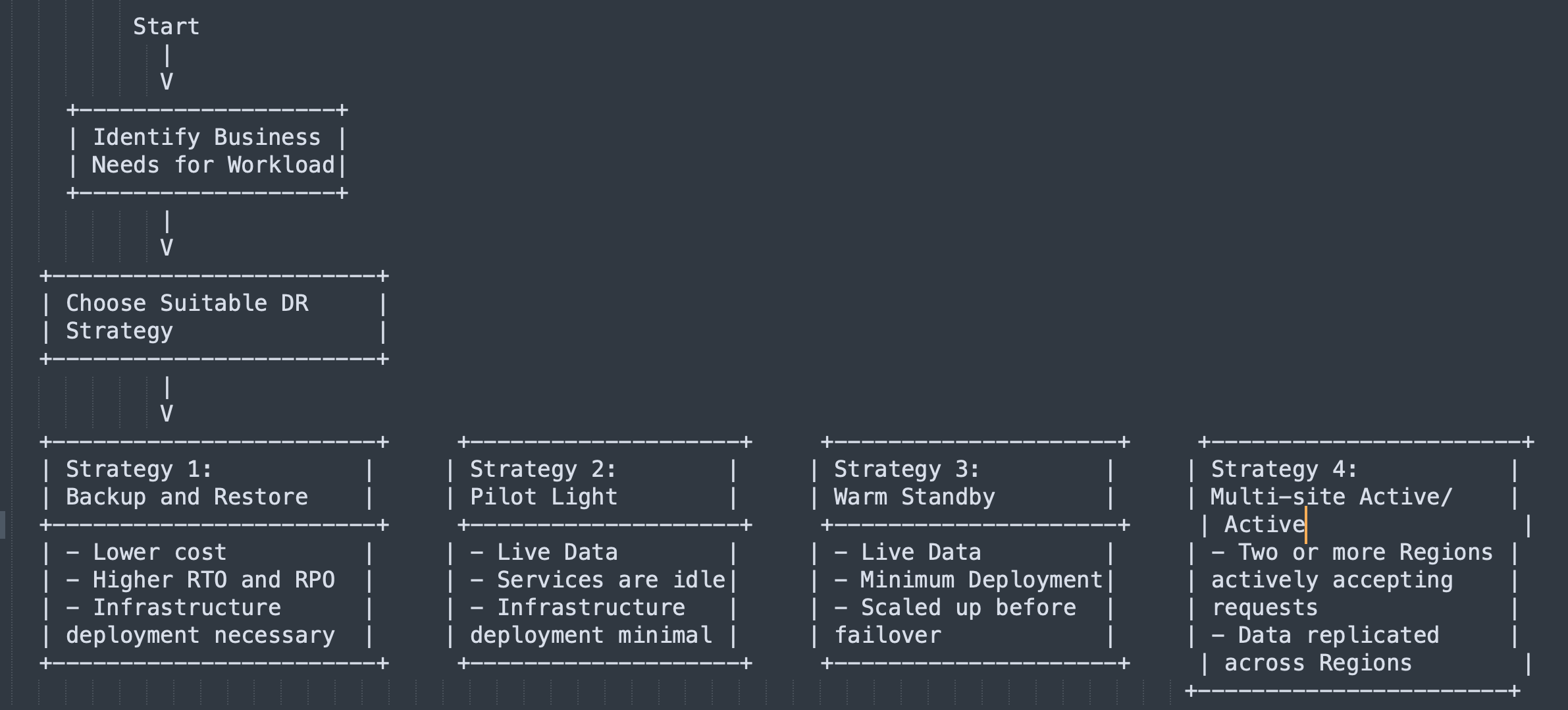
Implementing Disaster Recovery (DR) Strategies with Atsky: A Consultative and Strategic Approach
As the chief solutions architect for the Atsky's Robustness Framework, I aid clients in developing resilient workloads on AWS and Google...
Open page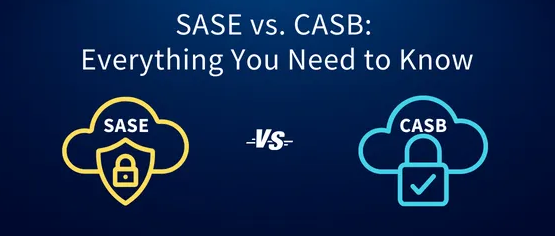
Navigating the Cybersecurity Landscape: CASB vs SASE
In our increasingly digital era, businesses are leaning more on cloud services and remote access. This shift has made cybersecurity not...
Open page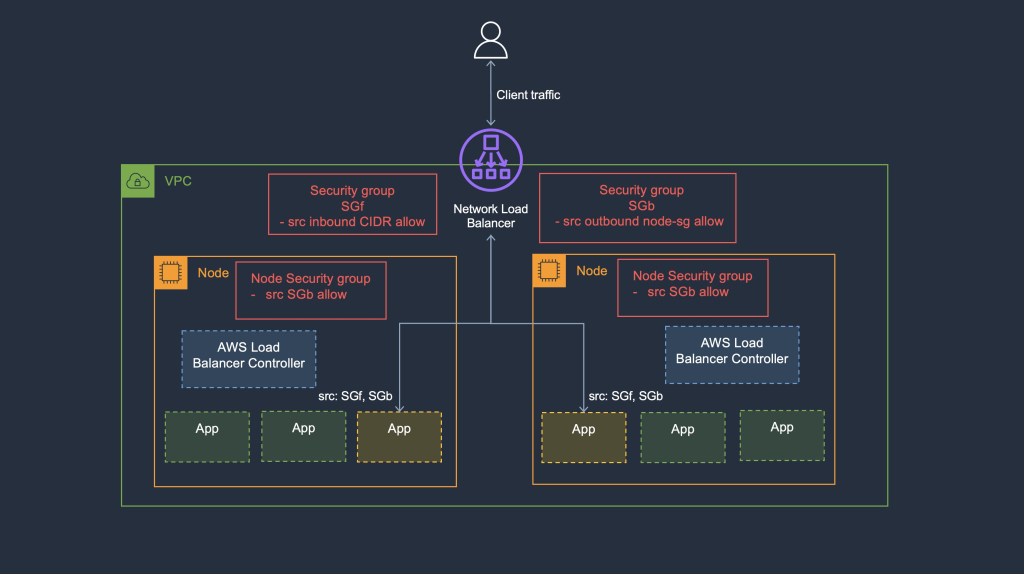
Exploring the New Support for Security Groups in Network Load Balancers
The realm of cloud computing witnesses constant evolution to cater to the dynamic needs of businesses. In a significant stride towards...
Open page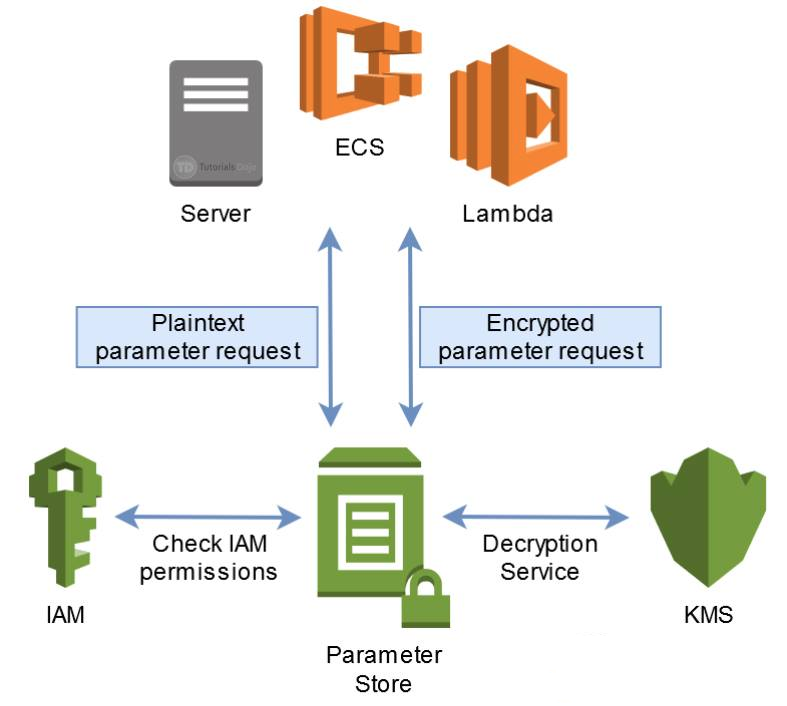
Secure Management of Database Credentials in an Amazon ECS Cluster
In today's era of cyber threats and stringent data privacy regulations, secure management of sensitive data such as database credentials...
Open page
Cloud Security Unlocked: Essential Best Practices for IAM in Cloud-Native Infrastructure
As businesses transition from on-premises infrastructure to cloud-based solutions, managing digital identities and access to resources...
Open page
Mastering AWS API Gateway with AWS APIGateway-integration: Practical Examples and Best Practice
API Gateway is a crucial component in modern application architectures, especially when building microservices or serverless...
Open page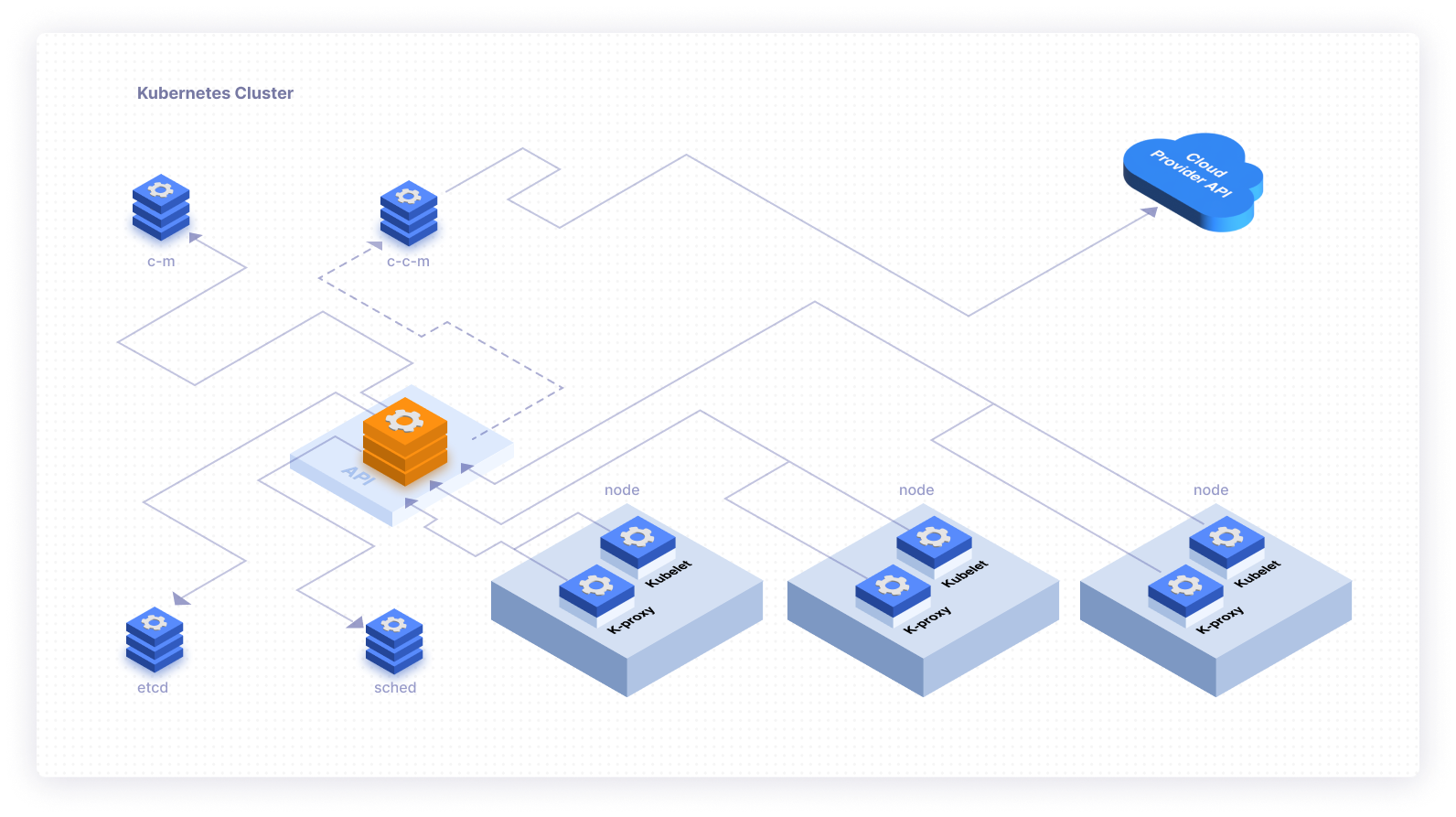
Getting Started with the Kubernetes API
Kubernetes has emerged as the leading container orchestration platform, which makes it easier to manage containerised applications at...
Open page
Enhance Debugging and Profiling: Node.js Logging Best Practices with Winston
Good logging practices are crucial for monitoring and troubleshooting your Node.js servers. They help you track errors in the...
Open page
12-Factor Methodology for Building Microservice Applications — On Kubernetes
Microservices have revolutionised the way we build and deploy applications, offering more resilience, easier scalability, and a more...
Open page
Strategies for ensuring data security in a cloud-native environment
In this post, we will refer to the three layers of infrastructure that make up cloud-native applications as the data plane, control...
Open page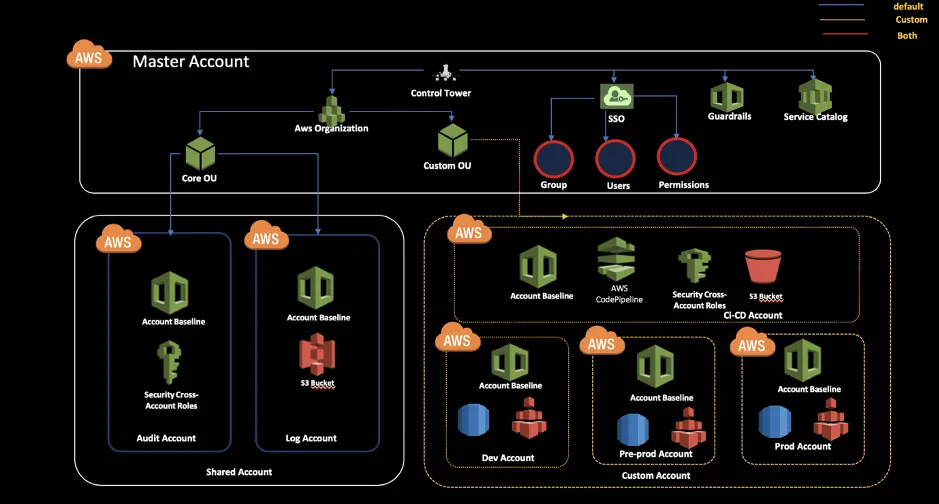
Ensuring secure residence of critical data workloads with network segmentation and Control Tower
In today's digital landscape, the secure residence of critical data workloads is of utmost importance for organizations. To achieve this,...
Open page
Ensuring GDPR Compliance and Data Protection in the Cloud
As hybrid working becomes the norm and more data is stored in the cloud, organizations face complex security challenges. To ensure that...
Open page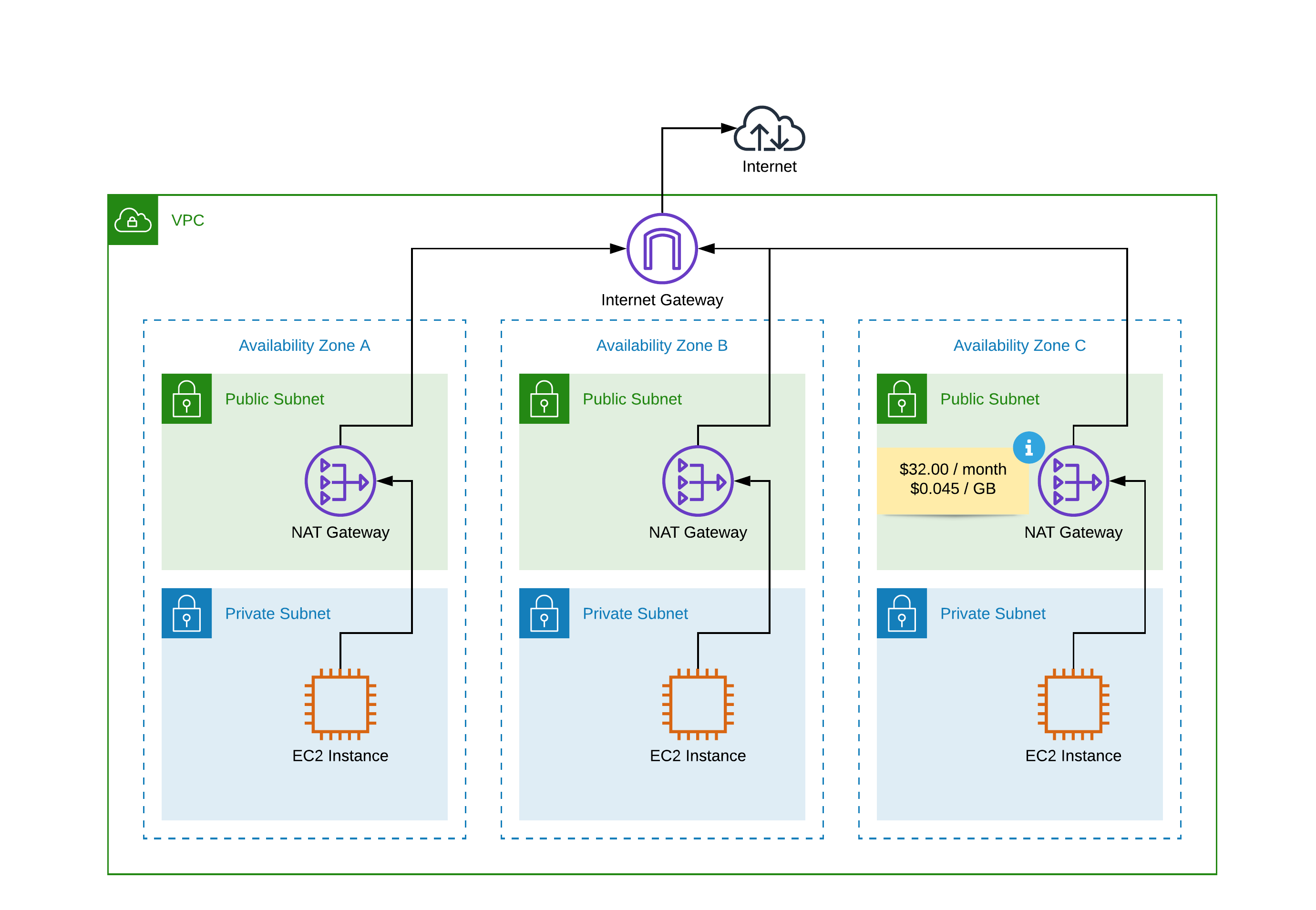
Understanding NAT Gateway for AWS: A Comprehensive Guide
What is a NAT Gateway and how does it work? NAT Gateway is an essential service that enables instances in a private subnet to connect to...
Open page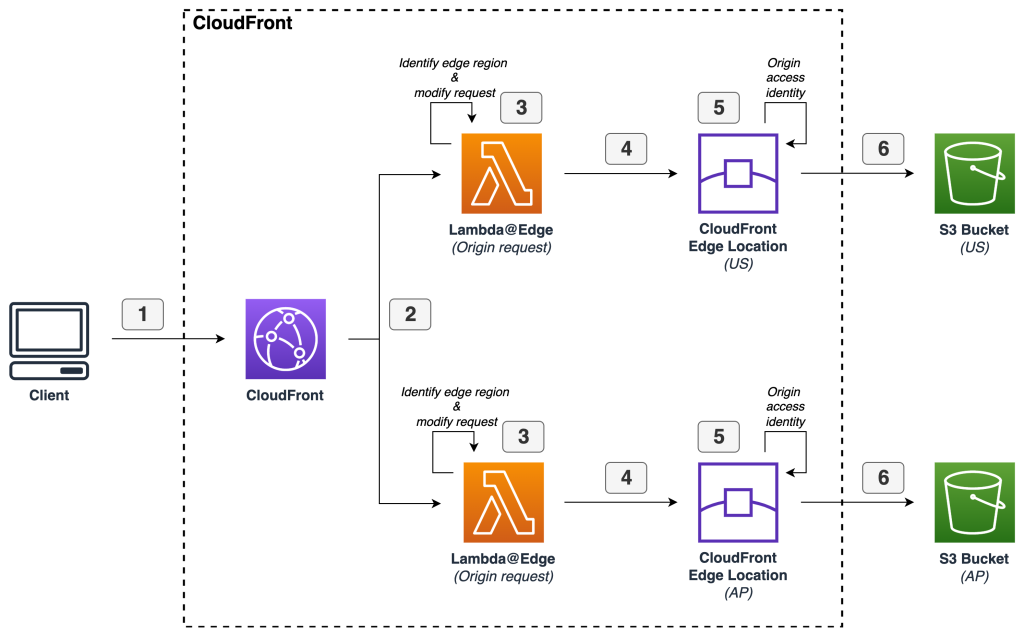
Optimising Application Performance with Amazon S3 Multi-Region Access Points and CloudFront
In a connected world, optimising application performance is a critical priority for enterprises, especially those catering to a...
Open page
Kubescape or Falco? Choosing the Right Kubernetes Security Tool for Your Environment
What is Kubescape? Kubescape is an open-source tool developed to scan Kubernetes clusters for security risks, including...
Open page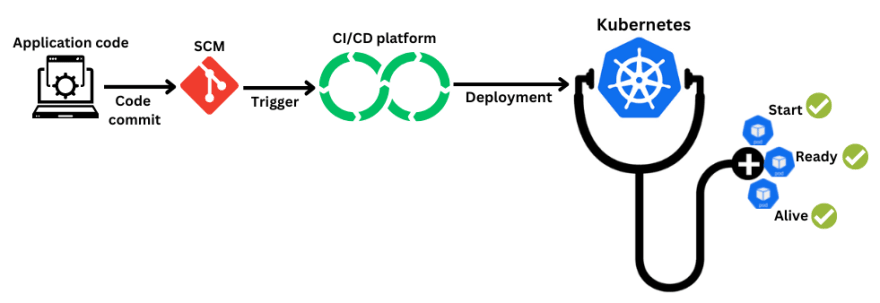
Configuring Kubernetes Probes for Effective Application Health Management
Kubernetes, an open-source container orchestration platform, revolutionises the deployment, scaling, and management of containerised...
Open page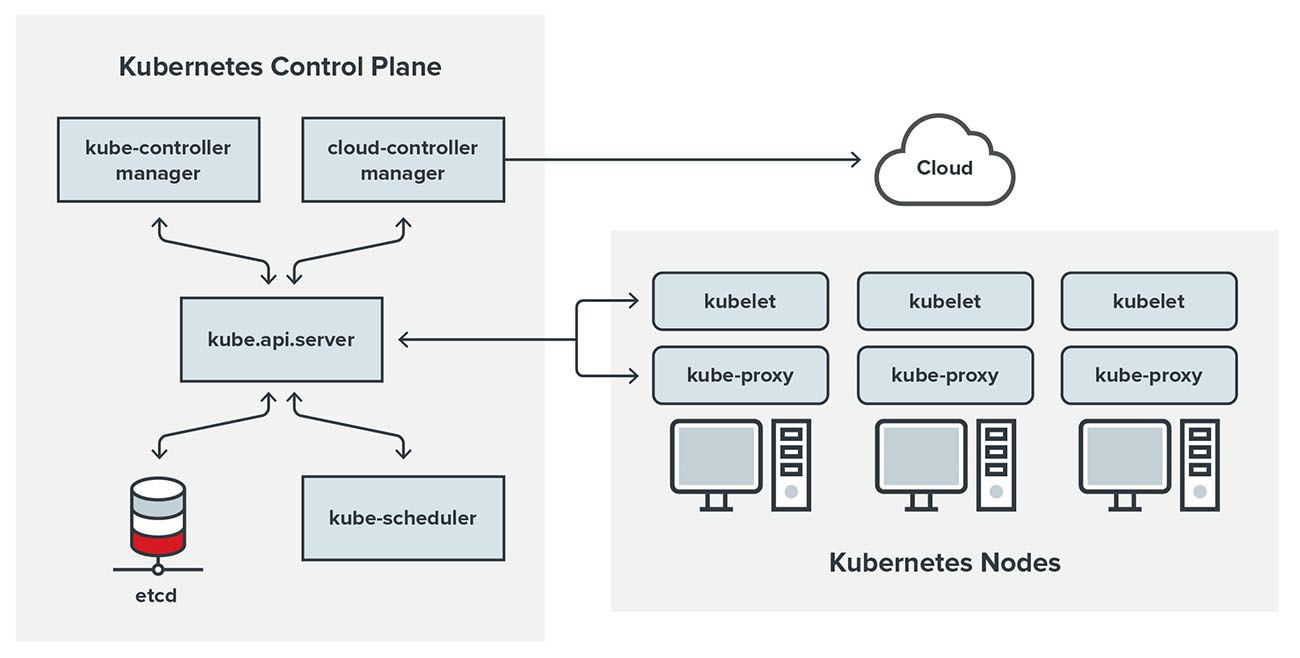
Security management in Kubernetes environment
Security management in Kubernetes environment is a critical aspect of any organization that uses Kubernetes for container orchestration....
Open page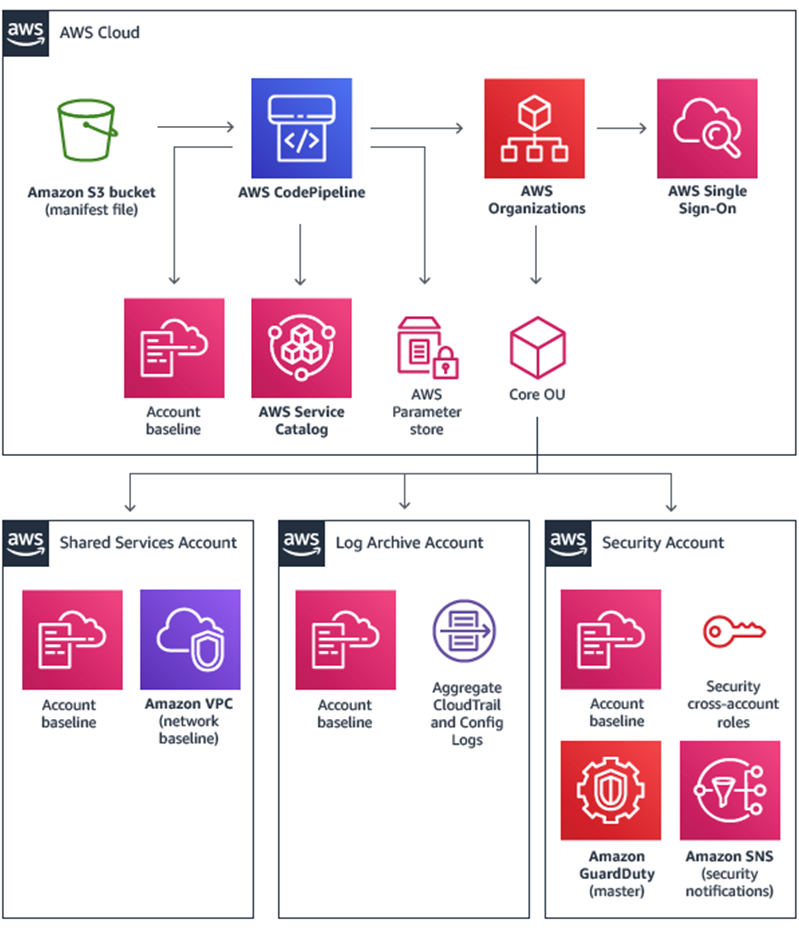
Creating a Secure Landing on AWS/Google: Optimal Strategies for Website Owners
As website proprietors, we comprehend the crucial significance of having a secure landing on AWS/Google. A well-secured landing page...
Open page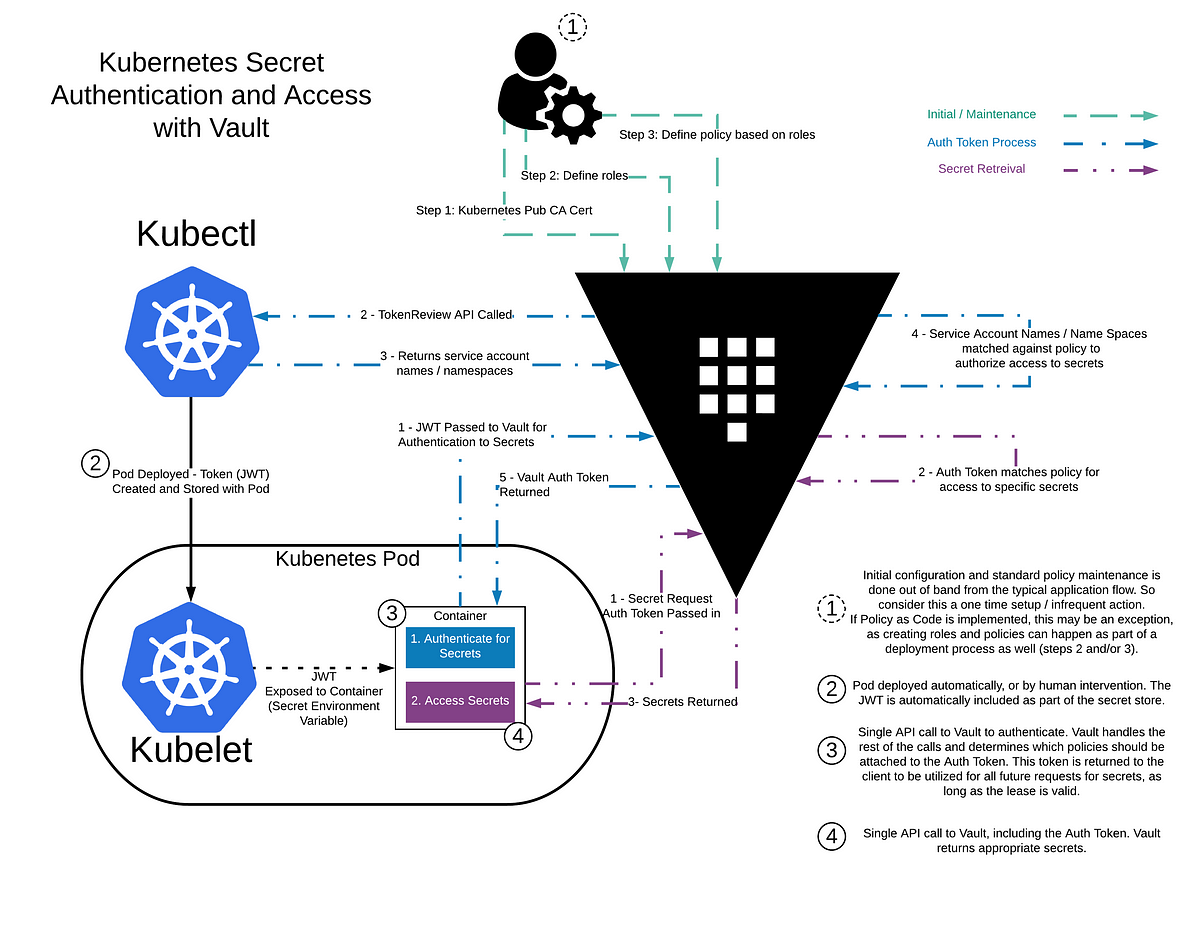
Secrets management in Kubernetes with Secret Manager or Vault
Secrets management is an essential aspect of any modern application development and deployment process. In the world of containerized...
Open page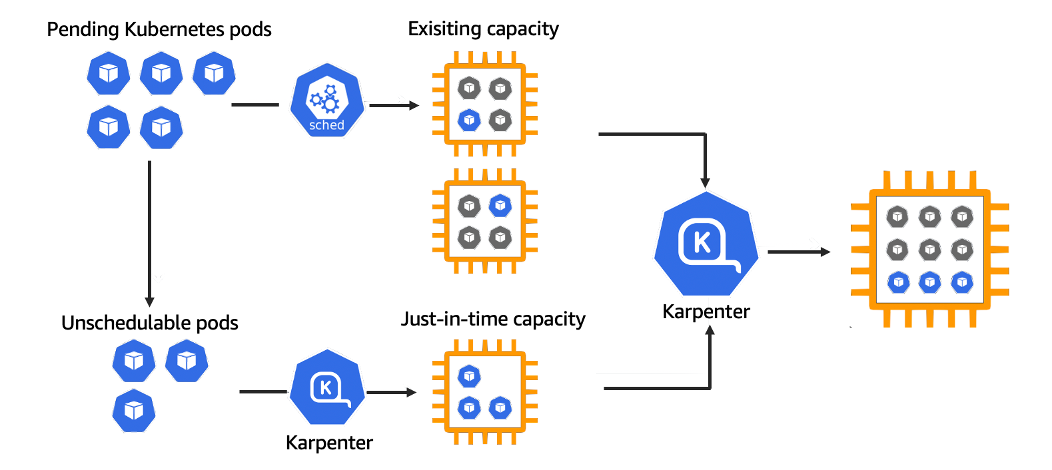
Achieving High Performance and Scalability with AWS Cluster Node Scaling using Karpenter
As the demand for cloud computing continues to grow, it has become increasingly essential to manage the capacity of interconnected nodes...
Open page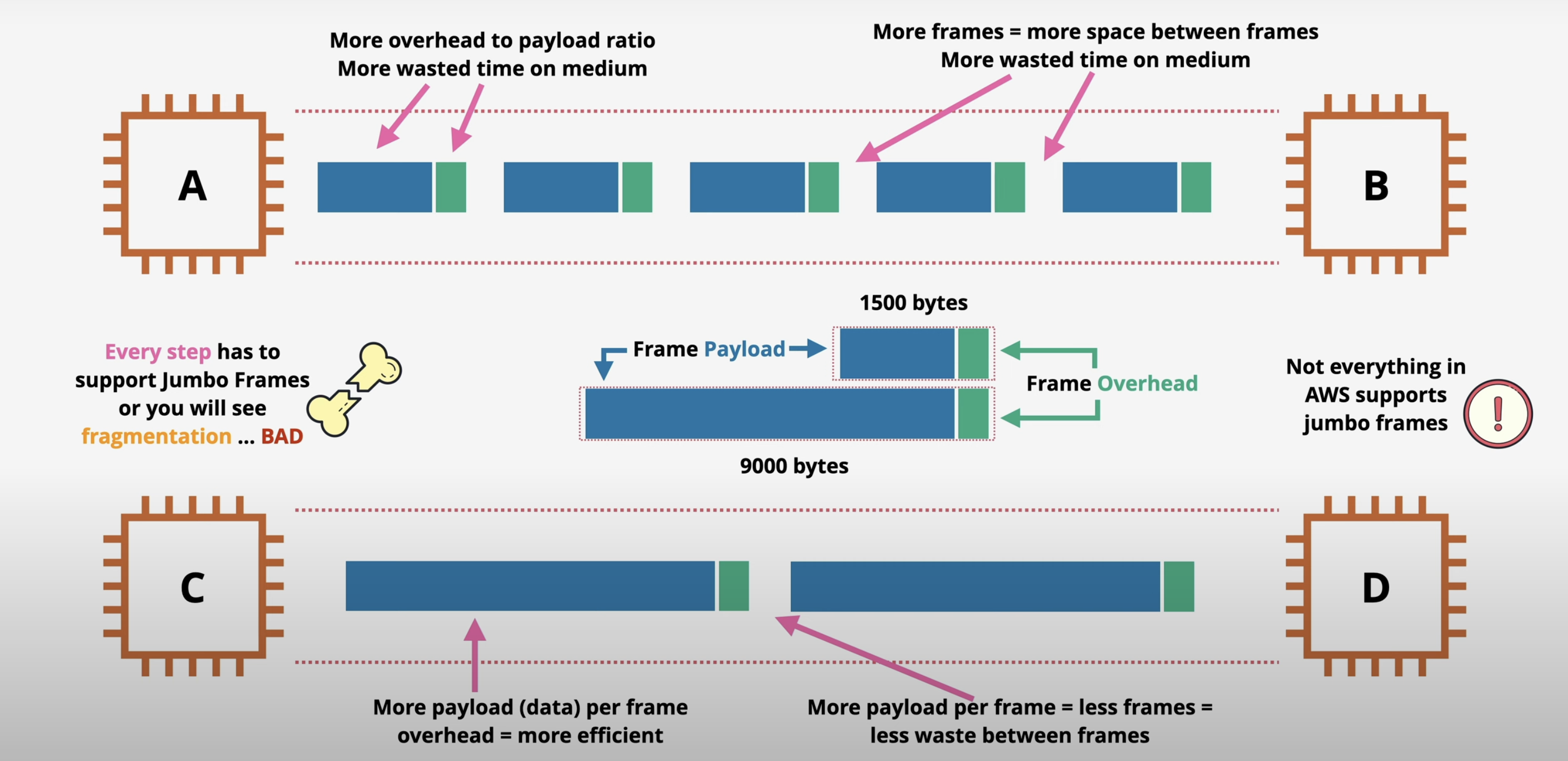
The Power of Jumbo Packets in Cloud Networks
Cloud networks are at the heart of modern applications and services, enabling businesses to deploy, manage, and scale their operations...
Open page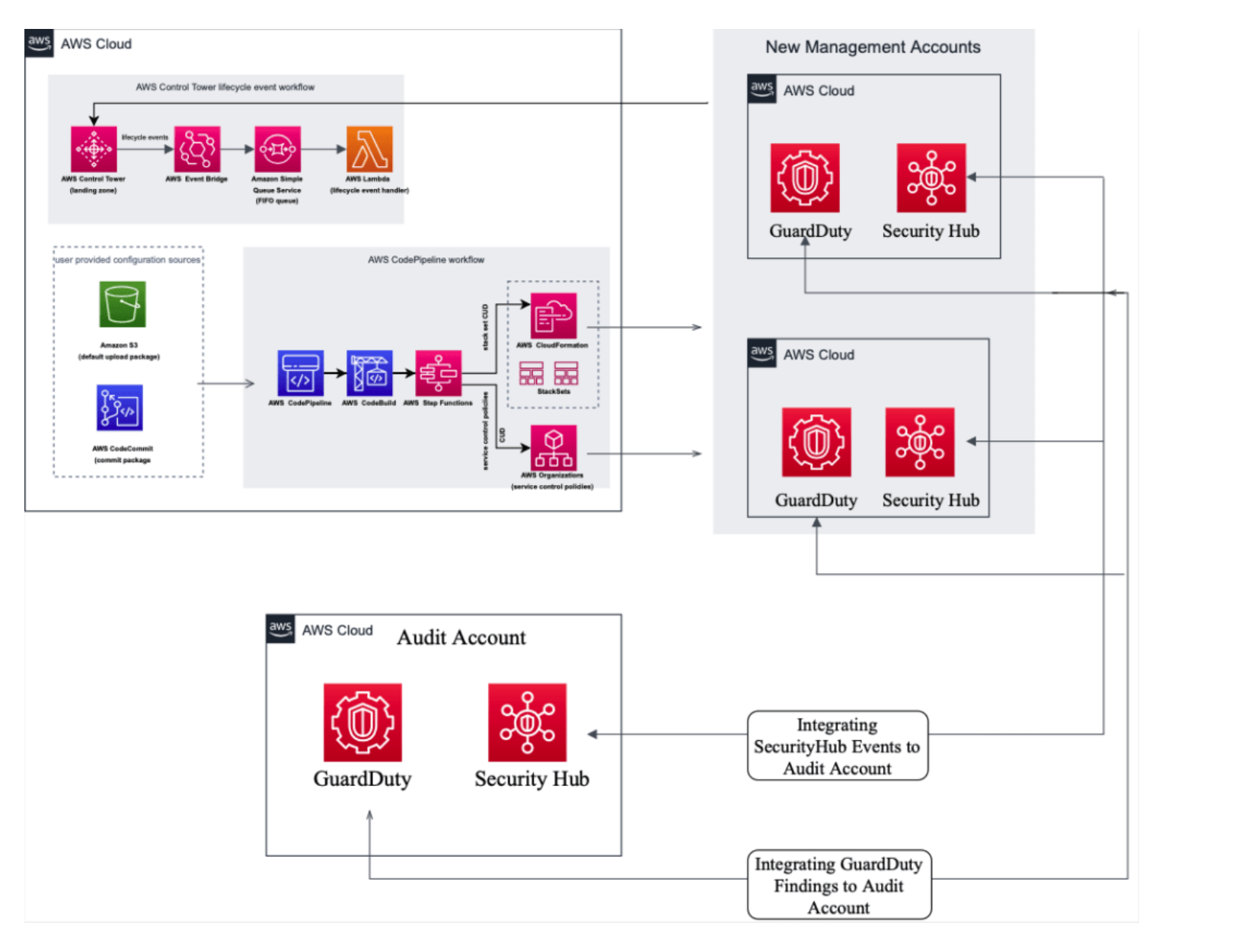
Integrating Security Hub with AWS Secured Landing Zone for Enhanced Security and Compliance
As more and more organizations are shifting towards cloud computing, it is essential to ensure that their infrastructure is secure and...
Open page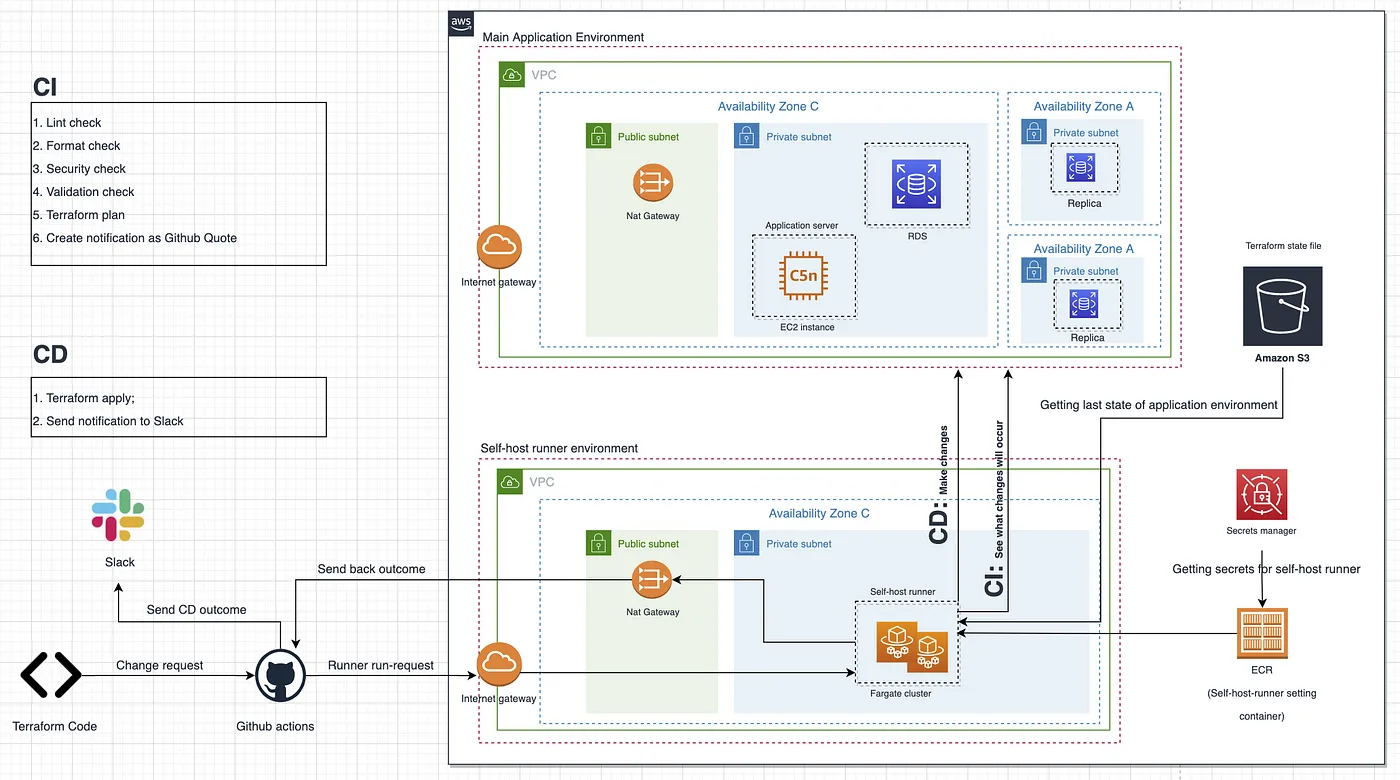
Self-hosted Git runners
Introduction Self-hosted Git runners are becoming increasingly popular for teams that require a robust continuous integration and...
Open page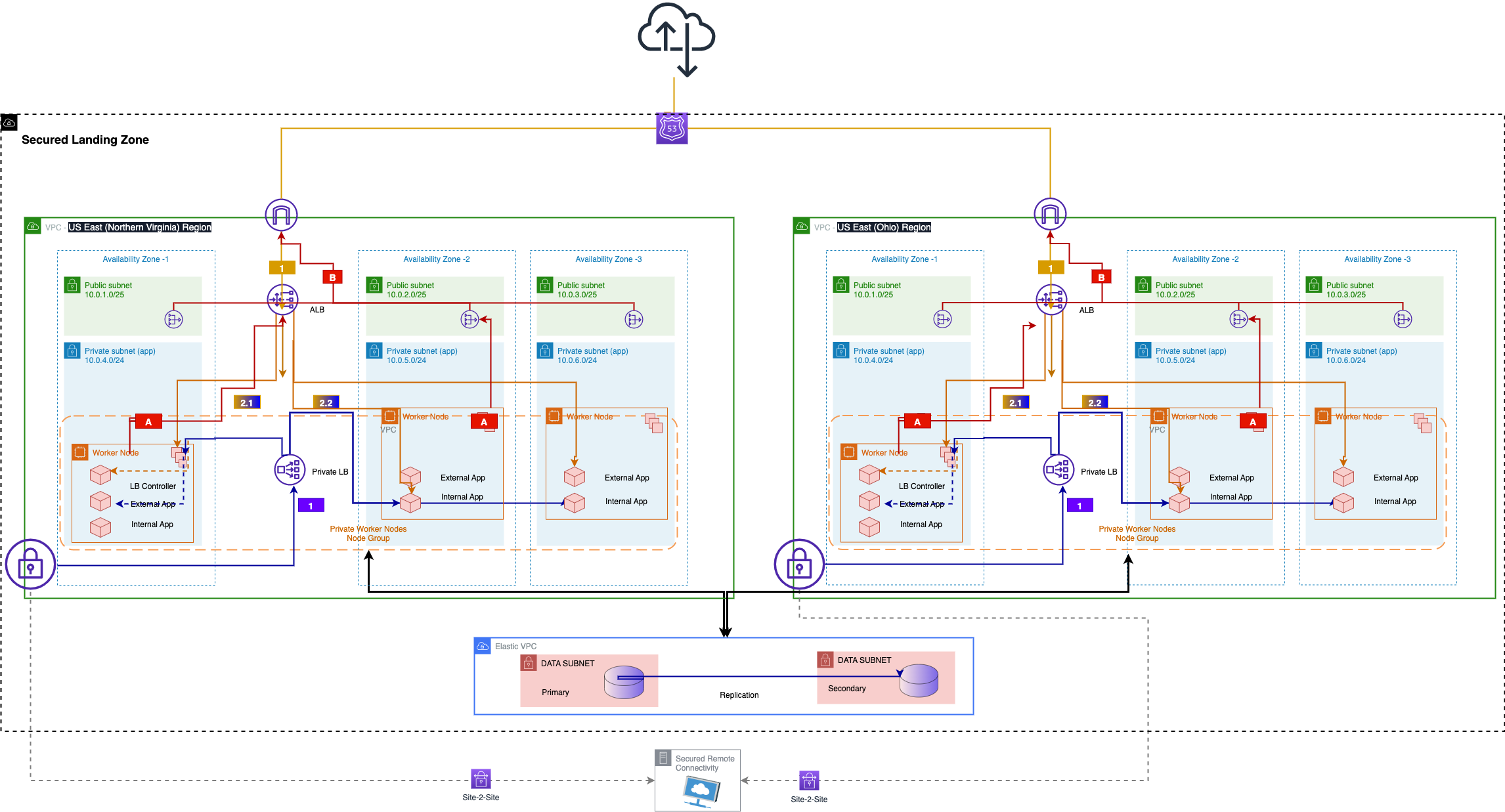
Building a Multi-AZ, Multi-Region Microservices Architecture with Amazon EKS
IIn the era of digital transformation, applications need to be scalable, resilient, and highly available to meet the demands of users...
Open page
How to Choose the Best Cloud Service Provider?
Introduction Choosing a public cloud service provider can be a challenging task, especially when there are so many options available. But...
Open page